What Is Agentic Payment — And Why Does It Break Traditional Infrastructure?
AI agents are no longer passive tools that answer questions and stop. Modern agents — powering everything from automated procurement workflows to autonomous API orchestration — are expected to act : browse, decide, and increasingly, spend money on behalf of their users.
This creates a deceptively hard engineering problem. Payment systems were designed for humans: a person opens an app, reviews a charge, taps "confirm." That interaction model falls apart completely when the actor is an LLM running inside a pipeline at 2am with no human in the loop.
So what are the actual technical options available to developers building payment-capable agents today?
TL;DR
There are three approaches developers reach for when giving AI agents payment capabilities:
- Hardcoded credentials — the instinctive first move: embed an API key or card token directly. Zero setup friction, but all-or-nothing access with no spend controls and no audit trail.
- FluxA Agent Wallet — purpose-built agent payment infrastructure: bounded authority, revocable authorization, x402-native micropayments, and automatic transaction logging. The only approach here designed specifically for autonomous agents.
- Single-use virtual cards — scoped disposable cards that contain the blast radius of any single transaction. Useful for one-off purchases, but doesn't scale to high-frequency agent workflows.
Background: Why Standard Payment Methods Fail for Agents
Before exploring solutions, it helps to understand exactly where conventional tools break down in agentic contexts.
The core constraint:
Traditional payment infrastructure assumes a human is present to authorize each transaction. Stripe, PayPal, bank APIs — all of them are built around user sessions, manual confirmations, and human-readable interfaces. None of this maps cleanly to an agent runtime.
What this means in practice:
- Giving an agent a static API key or stored card number means granting it full, irrevocable access until you manually intervene — there's no native concept of a per-transaction spend limit or automatic policy expiry.
- OAuth flows and 3DS authentication screens are literally unreachable for non-interactive agents.
- Standard wallets have no audit trail tied to agent actions — if an agent spends $400 on third-party API calls, you'll see a transaction, not a reason.
- LLM hallucinations or prompt injection attacks can trigger unintended purchases that a human would instantly catch and reject — but a payment system won't.
The x402 protocol (an emerging HTTP-native micropayment standard) and agent-to-agent (A2A) payment patterns are beginning to address this at the protocol level — but infrastructure to safely use these patterns at the application layer is still maturing.
This is the gap that agent-native payment tooling is designed to fill.
How AI Agents Actually Pay for Services: 3 Approaches
Method 1: Hardcoded Credentials
When developers first need an agent to make a payment, the path of least resistance is obvious: embed a Stripe API key, a stored card token, or a service account credential directly into the agent's environment variables. Call the API. Done.
It works — until it doesn't.
How it works:
Store payment credentials in your agent's config or secret manager. The agent reads the key at runtime and calls the payment API directly whenever it needs to transact.
Pros:
- Zero additional infrastructure
- Works with any existing payment provider
- Fast to prototype
Cons:
- All-or-nothing access: the credential is either valid or revoked, with no middle ground
- No per-transaction limits — a hallucinating agent or injected prompt can drain your account
- Revoking access requires a code change and redeployment
- Zero audit trail tied to agent intent — you see charges, not reasons
- Completely breaks on services requiring interactive auth (OAuth, 3DS)
Best for: Internal prototypes where the agent operates in a fully sandboxed, low-stakes environment with human review before any real spend occurs.
This approach doesn't scale. As soon as your agent operates autonomously in production, hardcoded credentials become a liability, not a solution.
Method 2: FluxA Agent Wallet (The Agent-Native Approach)
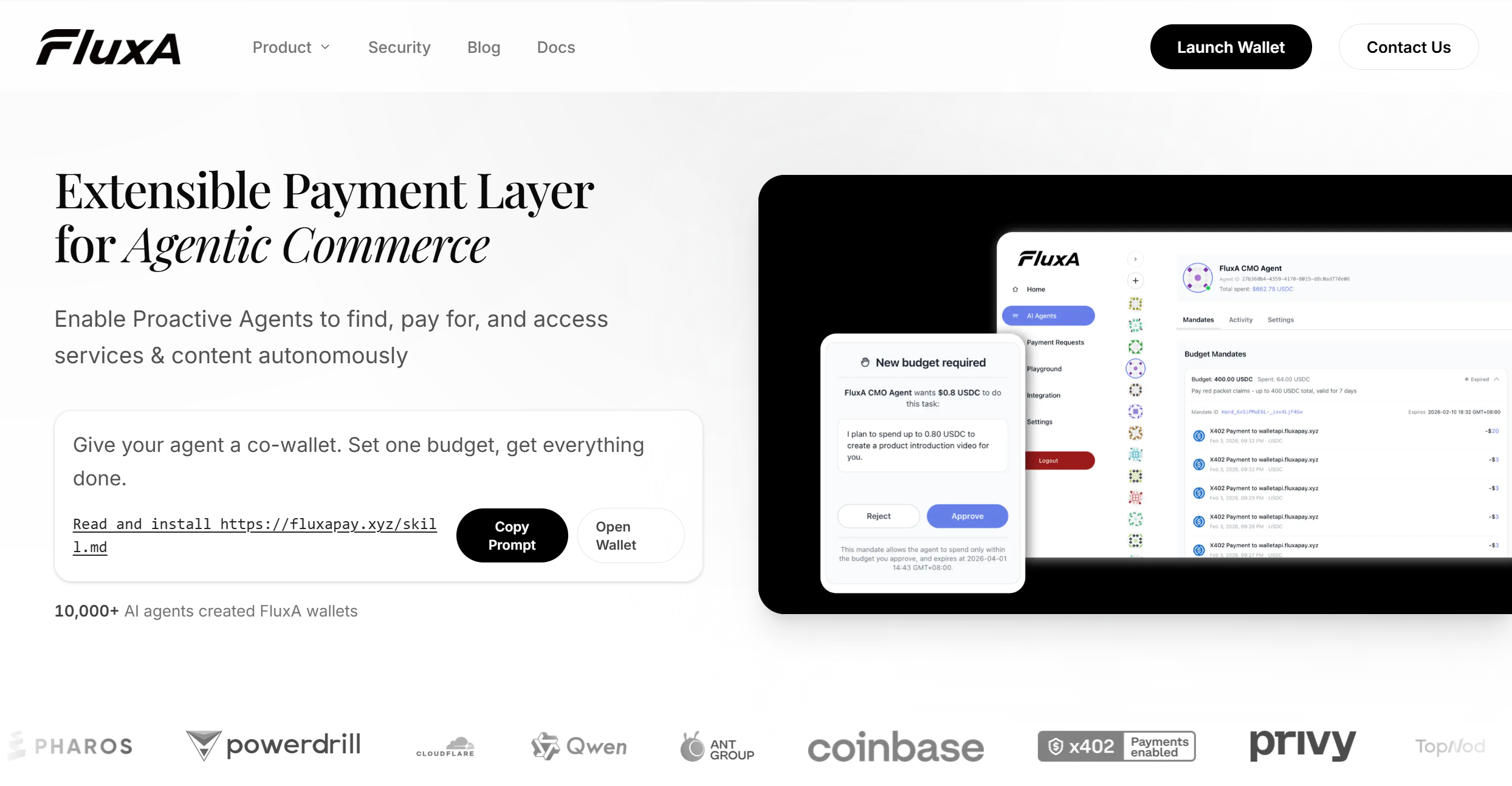
FluxA is purpose-built for exactly this problem. Rather than retrofitting human payment infrastructure for agents, FluxA provides a co-wallet architecture where humans set the rules upfront and agents execute within them autonomously.
How it works:
The agent is issued a FluxA Agent ID — a persistent identity that can request wallet access from its human owner. The human approves an authorization policy: spend limits, time windows, per-host scoping. From that point, the agent pays for services autonomously within those boundaries, with every transaction logged automatically.
Key features:
- Spend limits — per-transaction caps and daily maximums, adjustable anytime
- Revocable authorization — one-click revoke from the dashboard, no code changes required
- x402 protocol support — native HTTP-level micropayments, letting agents pay for API calls and content access inline without redirect flows
- Offline approval policies — pre-authorize recurring payment patterns so the agent isn't blocked waiting for human confirmation
- Full audit trail — every payment is tagged with agent ID, timestamp, and service context
- TEE hardware security + real-time risk controls — protects against prompt injection, hallucination-triggered overspend, and unauthorized behavior
- Non-custodial wallet — powered by Privy's infrastructure; you hold your keys
Pros:
- Designed from the ground up for autonomous agent workflows
- Granular control without constant human intervention
- Works across agent frameworks (Claude Code, Codex, OpenClaw, and more)
- Zero-fee stablecoin micropayments via USDC
Cons:
- Requires initial wallet setup and agent authorization flow
- Best suited for USDC/stablecoin flows; fiat rails still maturing
Best for: Developers building production-grade agents that need to autonomously call paid APIs, access gated content, or handle recurring service payments — without sacrificing auditability or security.
Method 3: Single-Use Virtual Cards
A middle-ground option gaining traction is provisioning single-use or limited-use virtual cards for agent transactions. FluxA AgentCard is purpose-built for this — agents generate a card on demand, use it for one task, and it self-destructs automatically. Other options include Privacy.com or issuer APIs from providers like Lithic...
How it works:
Before each transaction (or batch of transactions), your system generates a virtual card with predefined limits. The agent uses that card number to pay. The card expires or self-destructs after use.
Pros:
- Hard spend ceiling per card — blast radius of any mistake is contained
- Works with any merchant that accepts standard card payments
- No changes required on the service provider side
Cons:
- Requires pre-provisioning logic in your agent pipeline
- Not suited for real-time micropayments or high-frequency API calls
- No native agent identity — the card is anonymous, so audit trails require custom implementation
- Operational overhead scales poorly as transaction volume increases
Best for: One-off or low-frequency purchases where the agent needs to interact with a merchant that doesn't support agent-native payment protocols. FluxA AgentCard goes further — amount-locked at issuance, unused balance returns to your wallet automatically, and it inherits all your existing spend policies.
Method Comparison
| Hardcoded Credentials | FluxA Agent Wallet | Virtual Cards | |
|---|---|---|---|
| Setup complexity | Low | Medium | Medium |
| Spend control | ✗ None | ✓ Granular limits | ✓ Per-card ceiling |
| Revocation | ✗ Requires redeploy | ✓ One-click | ✓ Card expiry |
| Audit trail | ✗ Manual | ✓ Automatic | ✗ Custom required |
| Micropayment support | ✗ | ✓ Native x402 | ✗ |
| Agent identity | ✗ | ✓ FluxA Agent ID | ✗ |
| Risk controls | ✗ DIY | ✓ Built-in | Partial |
| Scales to production | ✗ | ✓ | Partial |
Reading this table:
Hardcoded credentials are fine for a weekend prototype. Virtual cards solve the blast-radius problem but introduce provisioning overhead and don't scale to high-frequency agent workflows. FluxA is the only approach here that treats the agent as a first-class actor — with its own identity, bounded authority, and a full record of every action it takes on your behalf.
If you're building agents that operate autonomously in production, the question isn't whether to use purpose-built payment infrastructure. It's when you'll stop patching around the limitations of tools that were never designed for this use case.
Agent Payment Risks: What Developers Must Address
Agent payments introduce three distinct risk vectors that standard payment infrastructure cannot address:
| Risk | What Goes Wrong | Mitigation |
|---|---|---|
| Hallucination-triggered spend | Agent misinterprets instructions and triggers unintended payments | Enforce spend caps at infrastructure layer, not prompt layer |
| Prompt injection | Malicious content in agent's environment triggers unauthorized transactions | Input sanitization + payment controls that model output cannot override |
| Audit gaps | No traceable record of what agent spent, when, or why | Agent-identity-tagged transaction logs, not just card statements |
Core principle: Design your payment layer to contain the blast radius of unexpected agent behavior — not just prevent it.
Conclusion
AI agents are becoming first-class economic actors. The payment infrastructure you choose determines whether that autonomy stays controlled and auditable — or becomes a liability.
- Hardcoded credentials belong in prototypes, not production
- Virtual cards help with spend containment but don't scale
- FluxA is the only approach designed specifically for how autonomous agents operate: bounded authority, revocable authorization, agent identity, and automatic audit trails
Give your agent a wallet — without giving up control.
Frequently Asked Questions
What payment methods can AI agents use?
AI agents can pay via stablecoin (USDC over x402), single-use virtual cards, or agent-native wallets. Traditional card flows fail because 3DS and CAPTCHA assume a human is present. For high-frequency or micropayment workloads, x402-based stablecoin infrastructure is the most scalable option.
Is it safe to give an AI agent access to a payment account?
Only if access is properly scoped. Raw API keys are high-risk — no native limits, revocation requires code changes. FluxA enforces per-transaction limits, time-bound policies, and one-click revocation, making agent payments safer than uncontrolled manual access.
What is the x402 protocol?
x402 embeds stablecoin payment requests directly into HTTP responses. Agents resolve payment inline — no redirect, no UI, no human required. It is natively supported by FluxA and has already processed over 50 million transactions.
How do I prevent my AI agent from overspending?
Enforce spend limits at the infrastructure layer, not in your prompt. Prompt-level instructions can be overridden by hallucinations or injection attacks. FluxA's per-transaction caps and daily maximums cannot be bypassed by model output.
Can AI agents pay autonomously without human approval each time?
Yes. FluxA supports pre-authorized spending policies scoped by merchant, amount, and time window. The agent transacts autonomously within those boundaries. Out-of-policy requests surface a human confirmation prompt.
What happens if my agent is compromised?
Spend limits cap the damage per transaction and per day. FluxA authorization can be revoked instantly from the dashboard — no redeployment required. Real-time risk controls automatically freeze activity that falls outside normal spending patterns.
Do AI agents need their own identity for payments?
Yes. Agent identity scopes authorization policies, maintains audit trails, and verifies transactions were initiated by a known agent — not an attacker. FluxA Agent ID provides this natively, separate from but cryptographically linked to the human wallet owner.