Agents Can Spend Money. Most Teams Have No Plan for That.
An AI agent that can book travel, purchase API access, reorder inventory, or pay for compute is genuinely useful. An AI agent that can do all of those things with no spending limits, no audit trail, and no revocation mechanism is an incident waiting to happen.
The problem is not that agents spend money. The problem is that most deployments treat spending authority as an afterthought — defined after the first incident rather than before deployment. Unlike a human employee who questions an unusual expense, an agent executes exactly what it is configured to do. If the configuration is wrong, the exposure compounds at machine speed.
TL;DR
AI agent spending controls are the policies, technical constraints, and infrastructure guardrails that define what an agent can spend, on what, and under what conditions — preventing unauthorized transactions, runaway costs, and compliance exposure.
| Core risk | Agents execute autonomously — overspending has no natural stopping point |
| 5 key controls | Spend limits, single-use credentials, approved service lists, human approval thresholds, audit logs |
| Who needs this | Any team deploying agents with transaction capability |
| Biggest gap | Most teams set controls at the session level, not the task level |
| Compliance angle | KYC/KYA frameworks now require agent-level transaction attribution |
Our take: Spending controls are not a security feature you add later. They are the prerequisite for giving an agent financial authority in the first place.
Why Agent Spending Is a Different Problem
Traditional expense management does not apply
Enterprise expense controls were designed around one assumption: a human initiates every transaction and can be held accountable for it. Approval workflows, receipt submissions, and monthly reconciliation all depend on that human in the loop.
AI agents break every part of that model:
- No natural pause points — agents do not stop to question whether a purchase is appropriate; they execute based on configuration
- High transaction frequency — a single agent workflow can trigger dozens of API calls or purchases within seconds
- No inherent accountability — without explicit logging, there is no record of which agent made which decision or why
- Cascading exposure in multi-agent systems — when Agent A delegates to Agent B, spending authority can compound across the chain without any single oversight point
The governance gap is already measurable
According to Cisco's State of AI Security 2026 report, while 83% of organizations planned to deploy agentic AI capabilities, only 29% felt truly ready to leverage these technologies securely. The gap between deployment pace and governance readiness is where spending incidents happen.
The stakes of getting this wrong are significant. According to Gartner, over 40% of agentic AI projects will be canceled by the end of 2027, due to escalating costs, unclear business value, or inadequate risk controls. Spending governance is not a compliance checkbox — it is a direct determinant of whether an agent deployment survives contact with production.
5 AI Agent Spending Controls Every Deployment Needs
1. Set Hard Spend Limits Per Task, Not Per Session
Most teams configure spending limits at the session level — a single budget cap for an entire agent workflow. The problem is that a session can contain dozens of discrete tasks, each with its own cost exposure.
Task-level limits are more granular and more protective:
- Each individual action has its own cap, independent of the broader session
- A runaway subtask cannot drain the session budget before other tasks complete
- Limits can be calibrated to the expected cost of each specific operation
In practice: A procurement agent booking travel should have separate limits for flight search API calls, hotel comparison queries, and the final booking transaction — not one shared pool that any single task can exhaust.
2. Use Single-Use Payment Credentials
Giving an AI agent a persistent credit card or reusable API payment token is one of the most common and consequential mistakes in agent deployment. A compromised agent with access to a live card number has uncapped spending ability until someone manually intervenes.
Single-use credentials solve this at the infrastructure level:
- Each transaction gets its own payment credential, funded for that amount only
- Credentials expire automatically once the transaction settles
- A compromised agent credential has zero residual value — the card is already closed
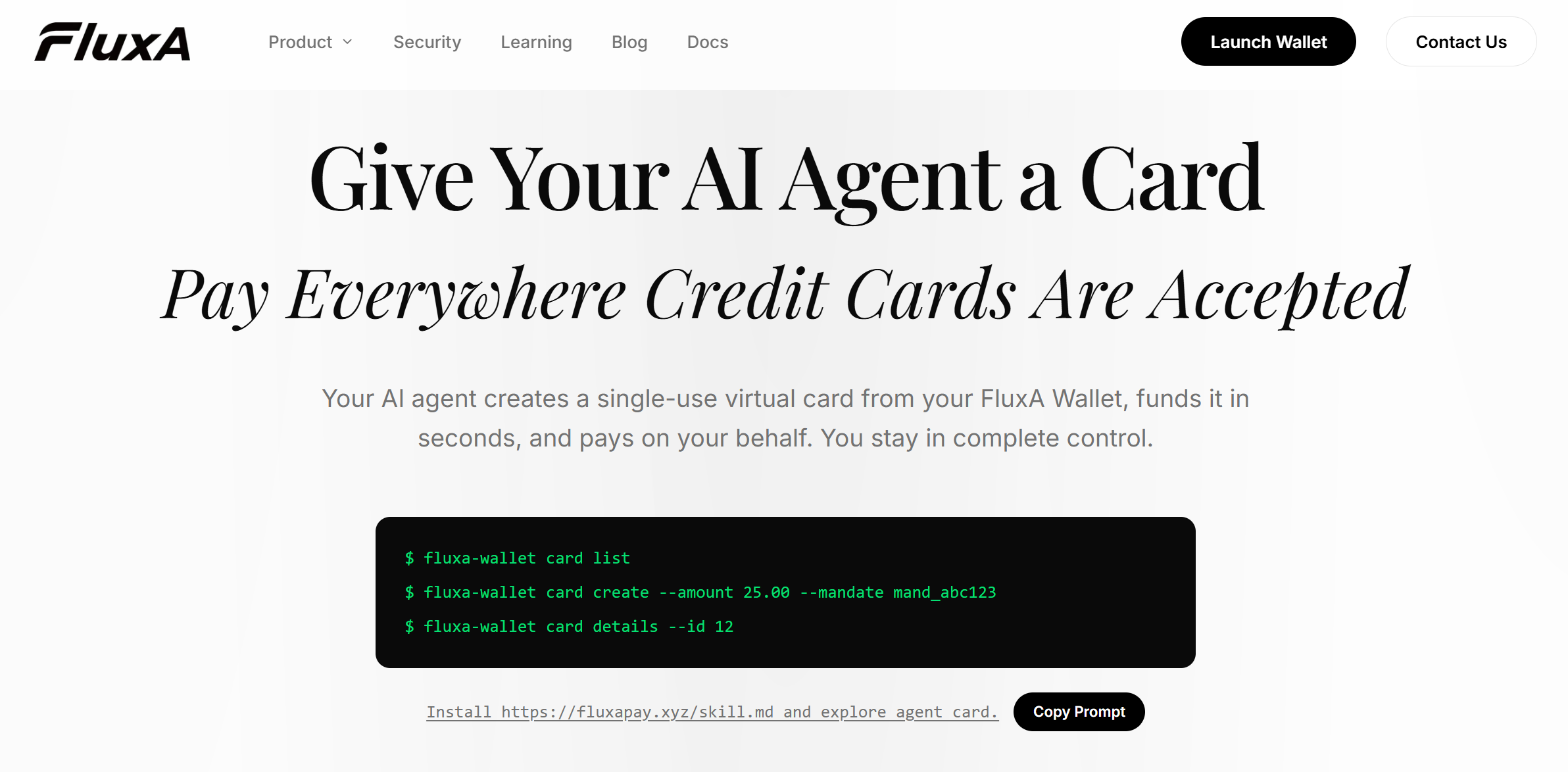
This is the core function of FluxA's AgentCard — a virtual card issued on demand from your FluxA Wallet, amount-locked per task, and automatically invalidated after use. The agent never touches your real payment credentials at any point in the workflow.
3. Define an Approved Service List Before Deployment
An agent with open internet access and payment capability can, in principle, transact with any endpoint it discovers. Without an approved service list, you have no control over which vendors or APIs your agent is paying.
A pre-deployment approved service list should include:
- Explicitly whitelisted API endpoints and vendors
- Spending caps per approved service
- A default-deny policy for any service not on the list
- A review cadence for updating the list as agent workflows evolve
Why this matters: Dynamic payment routing — where a server tells an agent where to send money — creates a surface for recipient manipulation. An approved service list closes that vector before deployment, not after an incident.
4. Require Human Approval Above a Transaction Threshold
Full autonomy is not always the right configuration. For high-value or irreversible transactions, a human approval gate is the most direct risk control available.
Effective threshold design:
- Set a hard dollar value above which the agent must pause and request approval
- Apply lower thresholds to new or unverified vendors
- Require approval for any transaction type the agent has not previously executed
- Log every approval request and outcome for audit purposes
According to McKinsey, the most responsible agentic commerce implementations keep humans in the loop for high-value or irreversible transactions — not because the agent cannot execute, but because the cost of a wrong decision at that value outweighs the efficiency gain.
5. Log Every Transaction With Agent Identity and Mandate Context
An audit trail is not optional for agents with spending authority. Without it, there is no way to investigate anomalies, demonstrate compliance, or attribute costs to specific agent actions.
A complete per-transaction log should capture:
- Agent identity — which agent initiated the transaction
- Mandate context — what task or workflow authorized the spend
- Timestamp, amount, recipient, and transaction outcome
- Any approval events or override actions taken
FluxA's AI Wallet records every card issuance, charge, and closure with agent identity and mandate context attached — giving teams a complete, queryable spending history without building custom logging infrastructure.
The 5 Controls at a Glance
| Control | What It Prevents | Implementation Level |
|---|---|---|
| Task-level spend limits | Budget exhaustion from a single runaway task | Configuration |
| Single-use credentials | Persistent credential exposure after compromise | Infrastructure |
| Approved service list | Unauthorized vendor payments and routing attacks | Policy |
| Human approval thresholds | Unchecked high-value or irreversible transactions | Workflow |
| Audit logs with agent identity | Uninvestigable anomalies and compliance gaps | Infrastructure |
Who Needs Spending Controls Most Right Now
Not every agent deployment carries the same risk profile. These are the teams where inadequate spending controls create the most immediate exposure.
AI agent developers building workflows that touch paid APIs, compute resources, or third-party services. Every external call that triggers a charge needs a credential strategy and a spend cap before it goes to production.
Enterprise procurement teams deploying agents to automate purchasing, vendor payments, or subscription management. The transaction values are higher, the compliance requirements are stricter, and the blast radius of a misconfigured agent is larger.
MCP server operators whose infrastructure is called by external agents. You are not just managing your own agent's spending — you are also responsible for ensuring that agents paying your endpoints are authorized to do so.
Developers building on x402 or AEP2 who need a payment credential layer that is compatible with protocol-level agent transactions without exposing persistent wallet access.
Conclusion
Getting spending controls right does not make an agent deployment safe. It makes it auditable, recoverable, and governable — which is the precondition for everything else.
The teams that ship agentic workflows successfully in 2026 share one trait: they defined the boundaries of agent authority before deployment, not after the first incident. Spend limits, credential hygiene, approved service lists, approval thresholds, and audit logs are not advanced features. They are the baseline.
According to Gartner, over 40% of agentic AI projects will be canceled by the end of 2027 due to escalating costs, unclear business value, or inadequate risk controls. Gartner The teams that avoid that outcome are not the ones with the most sophisticated agents — they are the ones who treated governance as infrastructure from day one.
If you are deploying agents that need to transact, FluxA provides the payment layer that implements controls 2 and 5 by default — single-use AgentCards for credential hygiene and a full audit trail via the FluxA AI Wallet. For protocol-level agent payments, the AEP2 protocol adds KYA compliance and mandate-governed settlement on top of x402.
Frequently Asked Questions
What are AI agent spending controls?
Spending controls are policies and technical guardrails that define what an agent can spend, with whom, and under what conditions. They cover spend limits, credential strategy, approved vendor lists, approval thresholds, and audit logging — all defined before an agent goes to production.
Why can't I just give my agent a prepaid card with a fixed balance?
A fixed-balance card solves overspending but not credential exposure. If the card details are compromised, they remain valid until manually canceled — single-use credentials that expire per transaction eliminate that residual risk entirely.
What is the difference between session-level and task-level spend limits?
Task-level limits are more granular and more protective than session-level caps. A separate limit per discrete action means one runaway subtask cannot exhaust the entire session budget before other tasks complete.
How do I handle spending in multi-agent workflows?
Each agent in the chain needs its own explicitly defined spend authority. Never pass payment credentials between agents — each should issue its own transaction-specific credential from a shared wallet, keeping the audit trail attributable at every step.
What is KYA and why does it matter for agent spending?
KYA (Know Your Agent) is the agent-era equivalent of KYC, requiring identity verification for AI transactions. As regulators treat agent transactions as auditable financial events, having agent identity attached to every spend record is moving from best practice to requirement.
Do spending controls slow agents down?
Well-implemented controls add negligible latency to agent workflows. Credential issuance and audit logging are near-instant — the only control that introduces deliberate delay is human approval thresholds, which is intentional for high-value transactions.