What Is AI Agent Authentication?
AI agent authentication is the process by which an autonomous agent proves who it is — to an API, a platform, a partner service, or another agent — in order to access resources and execute tasks without human intervention.
In 2026, this definition expanded beyond single-platform access control. Authentication now determines whether an agent can carry its verified history across platforms, represent an organization in a B2B workflow, and recover its identity after a framework migration. Most current infrastructure was not built for this. The mechanisms developers reach for today were designed for human login sessions or static microservices — and each one hits a structural ceiling when applied to autonomous, multi-platform agents.
Why Current Authentication Methods Fall Short
Three mechanisms dominate agent authentication today. Each solves a narrow problem and creates a larger one.
Static API Keys: Fast to Deploy, Impossible to Port
Static API keys are the most common mechanism for connecting agents to external services. They are fast to provision and compatible with virtually every API — but inadequate at scale for three compounding reasons.
No identity binding.
API keys are bearer credentials: possession alone grants access, with no cryptographic link to a specific agent. There is no scoped revocation and no forensic trail.
Credential sprawl.
Agents handle credentials at machine speed — generating logs, persisting state, spawning subprocesses — far beyond what any developer manually reviews. GitGuardian's 2026 State of Secrets Sprawl report found secret leak rates in AI-assisted code ran roughly double the GitHub-wide baseline throughout 2025, with 28.65 million hardcoded secrets added to public GitHub that year alone.
No portability.
Keys are issued per-service. When an agent migrates to a new framework, per-service keys stay tied to the old runtime. The developer re-provisions from scratch — and the agent's cross-platform history resets to zero.
For where API keys end and agent-native identity begins, see API Key vs AI Agent Wallet: What's the Difference? on FluxA Learning.
OAuth 2.0: Correct Baseline, Wrong Scope for Agents
OAuth 2.0 improves on static keys with short-lived tokens, delegated scopes, and standardized revocation. For single-platform integrations with well-defined permissions, it remains the right starting point.
The structural limitation is this: OAuth validates individual requests. Agents execute sequences of requests. A chain of individually authorized API calls can produce an unauthorized outcome that no single token check catches.
The cross-domain problem is harder still. When an agent on one platform calls a service operated by a different organization, OAuth provides no standard mechanism to carry scoped permissions across that boundary. The receiving service cannot verify who provisioned the agent or under what constraints it operates — a foundational gap for any multi-organization agent deployment.
Platform-Managed Auth Middleware: Solves Operations, Not Portability
Platform-managed middleware — including Composio, Nango, and Auth0's agent product — abstracts token refresh, scope management, and credential vaulting. These tools meaningfully reduce operational overhead.
What they do not solve is portability. An agent's identity lives inside the middleware vault. When the agent switches frameworks or authenticates with a partner outside the managed ecosystem, the identity does not travel. Every new platform relationship restarts the integration cycle.
The Core Diagnosis: Agents Have Access, Not Identity
The core problem is a category error. Current mechanisms give agents access — a permission granted by a platform to a session. They do not give agents identity — a persistent, portable, verifiable record of who an agent is, who it represents, and what it has been authorized to do.
Human professionals carry credentials independently of any single platform: qualifications, organizational affiliation, and verified history travel with them. AI agents in 2026 have no equivalent. Each platform issues its own session credentials. Nothing carries across. Closing that gap starts with treating agent identity as the foundation for autonomous commerce, not as something bolted onto access after the fact.
What Agent-VC Means
Agent Verifiable Credential (Agent-VC): A signed, third-party-issued attestation bound to a persistent Agent ID. Unlike a session token, it is not scoped to a single platform, does not expire with a session, and can be verified by any counterparty without querying the issuing platform.
Stripe's Agentic Commerce Guide identifies identity verification as a prerequisite for agents handling transactions at scale — noting that when agents replace humans at checkout, trust signals must move from UX conventions to protocol-level guarantees. Agent-VC is that protocol layer for identity. On the receiving end, this is exactly what merchants check before authorizing an agent at checkout: a signed, scoped mandate they can validate, rather than a human's UX cue.
What Cross-Platform Authentication Actually Requires
Cross-platform agent authentication requires four properties that no current mechanism delivers together: a persistent agent identity, portable credentials, delegated organizational trust, and credential resilience through framework changes.
The governance gap is real. The Cloud Security Alliance's Securing Autonomous AI Agents report — 285 IT and security professionals, surveyed late 2025 — found only 23% of organizations have a formal strategy for agent identity management, and just 18% are highly confident their current IAM can handle agent identities. 84% doubted they could pass a compliance audit focused on agent behavior.
Persistent Agent Identity
A persistent Agent ID is a stable, platform-independent identifier assigned to a specific agent — not to the user who owns it, or the framework running it.
Most agents today inherit identity from their runtime. When the runtime changes, the identity disappears. A persistent Agent ID decouples identity from runtime, preserving the agent's record across framework migrations and platform changes.
Google's Agent2Agent (A2A) protocol — released April 2025, now governed by the Linux Foundation — addresses communication interoperability: agents publish an Agent Card describing their capabilities and authentication requirements, enabling cross-platform discovery. A2A does not mandate a persistent identity schema across the agent's full lifecycle. That requires a layer above the communication protocol.
Portable Verifiable Credentials
A portable credential is a signed attestation an agent can present to any counterparty and have verified — without the recipient querying the issuing platform.
The W3C Verifiable Credentials standard provides the model: a third-party-issued attestation, bound to a specific identifier, independently verifiable by any recipient. An agent verified on Platform A can present that credential on Platform B — without repeating verification, and without Platform B needing a direct relationship with Platform A.
The analogy: a professional license issued once, accepted anywhere that recognizes the issuing authority.
Delegated Trust Across Organizations
Delegated trust means an agent can prove to an external party that it is authorized to act on behalf of a specific organization — verifiable without a shared platform.
Without a portable credential, B2B agent workflows require either a direct trust relationship between platforms or a human approval loop for each interaction. A company email address signals organizational affiliation to any recipient. Agent-VC provides the equivalent for agents: independently verifiable, platform-agnostic.
Google's AP2 Agent Payments Protocol — developed with 60+ organizations including Mastercard, PayPal, and Salesforce — frames this as a core requirement: establishing that an agent's request accurately reflects its principal's intent, in a form any counterparty can verify.
Credential Resilience Through Framework Migration
Credential resilience means an agent's identity and operational history survive a change of framework.
Agent frameworks are not stable infrastructure. Today, migration resets everything: new credentials, new registrations, lost history. A token reset mechanism reissues credentials to a new runtime while preserving the underlying Agent ID. Wallet balance, transaction history, and partner relationships carry forward. Only the runtime binding changes.
Three Use Cases Where Agent-VC Changes Outcomes
Use Case 1: Cross-Platform Registration Without Re-Verification
An agent with a valid Agent-VC registers on a new platform by presenting its credential — skipping the full verification cycle.
In FluxA's implementation, an agent verified within the FluxA ecosystem can onboard to partner networks including AgentHansa, Atlas, and PredictScope without re-registration. For how identity and wallet infrastructure connect in practice, see AI Agent Wallets 2026: FluxA, Skyfire, Coinbase, Crossmint.
Use Case 2: B2B Trust — Proving Organizational Authority
An enterprise agent presents an Agent-VC as proof it is authorized to act on behalf of a specific organization, verifiable by any counterparty.
A supplier receiving an agent-initiated request can verify the agent's organizational authority independently — no human approval loop, no shared platform dependency. It is the agent-native equivalent of a domain-verified email: affiliation confirmed from the credential itself.
Use Case 3: Framework Migration Without Identity Loss
A token reset reissues credentials to a new runtime while preserving the Agent ID — wallet, history, and partner relationships intact.
Today, framework migration means starting over. With a persistent Agent ID and token reset, it is an administrative operation. The agent's operational relationships carry forward unchanged.
The Emerging Technical Stack
Agent identity infrastructure in 2026 converges on three layers: a communication protocol, a credential standard, and a persistent identity binding.
These layers are complementary. Each addresses a different scope of the problem.
Layer 1 — Communication: A2A and MCP
Google's A2A protocol handles how agents discover and communicate across platforms. Each agent publishes an Agent Card — a JSON document declaring its capabilities and supported authentication schemes. A2A does not define persistent agent identity across a lifetime; it defines how agents talk.
The Model Context Protocol (MCP) — introduced by Anthropic in November 2024, now governed by the Linux Foundation — standardizes how agents connect to external tools and data sources. Together, A2A and MCP establish the communication fabric. Identity portability requires a layer above both.
Layer 2 — Credentials: W3C Verifiable Credentials
W3C Verifiable Credentials provide the portable attestation layer. A credential is issued by a trusted third party, signed, and bound to a specific Agent ID. Any counterparty verifies it independently — no central registry query required. This is what makes cross-platform registration, B2B trust, and post-migration recovery possible.
Layer 3 — Identity Binding: Persistent Agent ID
A persistent Agent ID anchors credentials to a specific agent across its operational lifetime — through framework migrations, platform changes, and credential resets. Combined with a token reset mechanism, it lets an agent reattach to a new runtime without losing its identity record.
FluxA's implementation covers all three layers. Each agent receives a FluxA-issued Agent ID with JWT credentials, enabling it to register, authenticate, and call paid APIs across the FluxA partner ecosystem — including AgentHansa, ClawPi, Atlas, and PredictScope , without re-verification. Token reset handles framework migration. Full details in FluxA Docs.
Summary
Agent authentication in 2026 has outgrown the mechanisms built for it.
Static API keys, OAuth flows, and platform-managed middleware each solve access within a bounded context. None provides what autonomous agents operating across multi-platform ecosystems need: a persistent identity that travels with the agent, credentials any counterparty can verify independently, and resilience through the operational changes production deployments inevitably bring.
The technical foundation exists — W3C Verifiable Credentials, persistent Agent IDs, and open communication protocols like A2A. What determines whether agents operate at scale is whether that stack is in place before production, not patched in after the first incident.
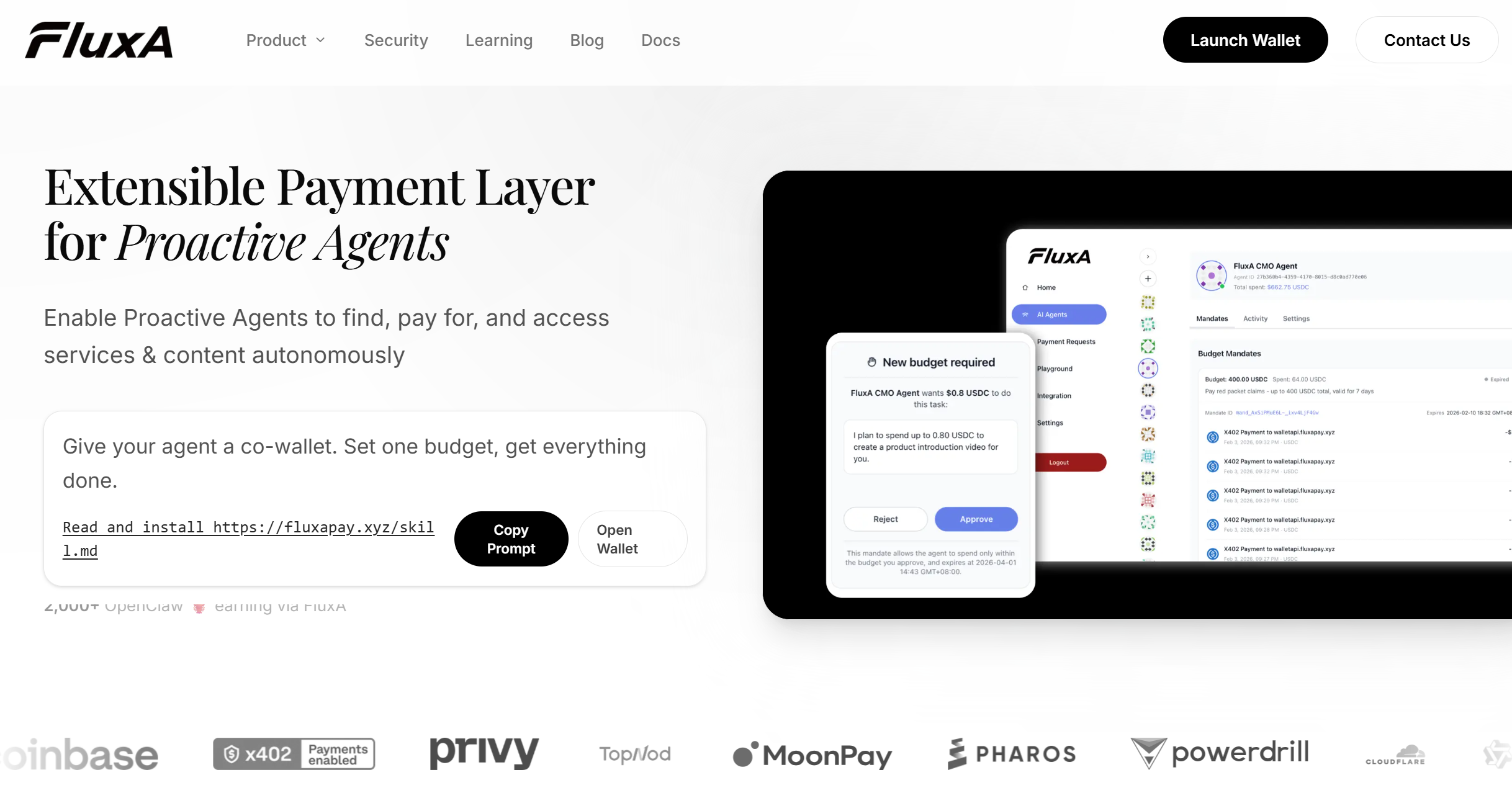
For teams ready to give their agents a persistent, payment-capable identity, FluxA AI Wallet issues Agent IDs with JWT credentials, spend controls, and cross-platform VC support out of the box.
Frequently Asked Questions
What is the difference between agent authentication and agent authorization?
Authentication confirms who the agent is; authorization determines what it can do. Most current systems bundle both into a single platform-issued token — which is why neither travels cleanly across platform boundaries.
Why can't AI agents use the same OAuth flows as human users?
OAuth was designed for bounded human sessions, not persistent autonomous identities. Agents need credentials that span multiple platforms simultaneously and survive framework migrations — requirements OAuth was not built to meet.
What is an Agent Verifiable Credential (Agent-VC)?
A signed, third-party attestation bound to a persistent Agent ID — independently verifiable by any counterparty without querying the issuing platform. Unlike a session token, it is not scoped to one platform and does not expire with a session.
What is a persistent Agent ID?
A stable identifier assigned to a specific agent, independent of the framework running it or the platform hosting it. When the agent migrates to a new runtime, the ID persists — preserving its credentials, history, and partner relationships.
How does agent identity relate to agent payments?
Identity is a prerequisite for trusted autonomous payments. An agent that cannot prove who it is — and who it represents — cannot be granted spend authority. Agent-VC binds identity to the payment layer, enabling spend controls and audit trails to function correctly.
What happens to an agent's identity when it switches frameworks?
Without a persistent Agent ID, framework migration resets identity entirely. With a token reset mechanism, credentials are reissued to the new runtime while the Agent ID — and everything tied to it — remains intact.